by Yasir Altaf Zargar
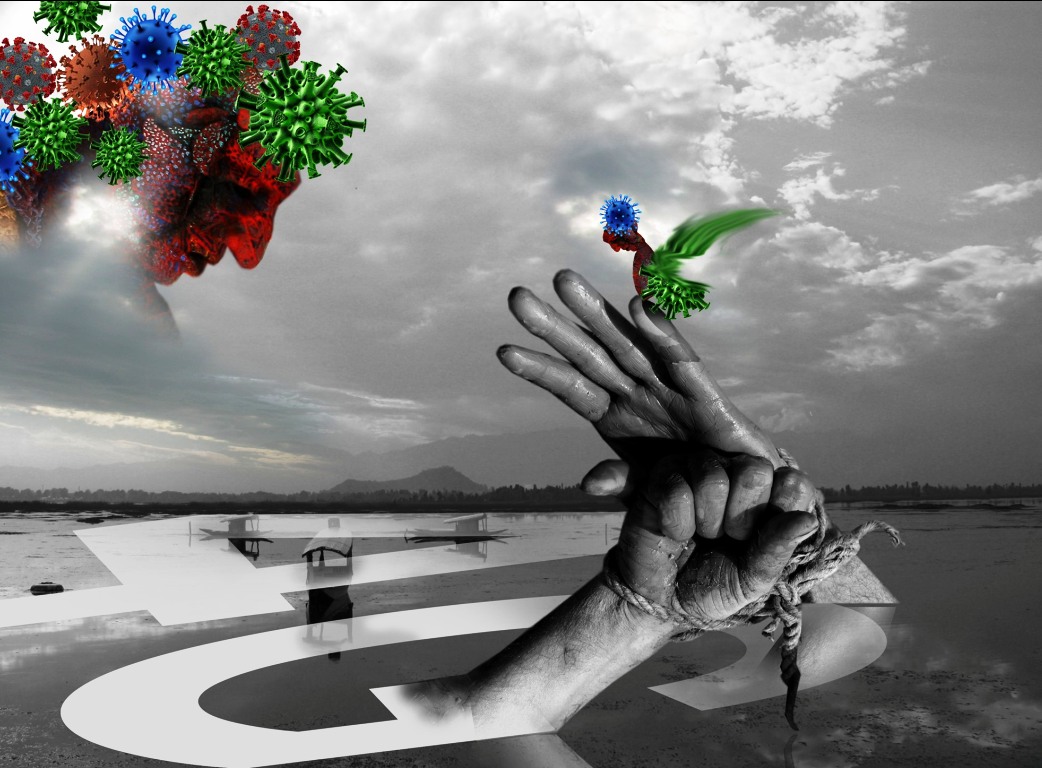
With the outbreak of Covid-19 causing an unprecedented global halt, billions of people across the globe have been sent to self-isolation and social distancing, with official lockdown procedures in place at multiple locations. As a result, the culture of working and studying from home has been promoted heavily as long as internet connectivity is not an issue. The Covid-19 pandemic has fostered a need in people across the world to operate in new ways, making all the necessary adjustments to survive through this pandemic. One of such new adjustments and measures involves people opting for virtual services to compensate for the lack of physical mobility and access at the present time. The virtual services that emerge from the internet have instantly become a key facilitator to counter the outbreak of Coronavirus while also being an effective channel of human interaction amid imposed social distancing.

While these virtual services have, to a limited extent, enabled the operation of businesses, government offices and schools by bridging basic communication gaps, a sinister side of illegal usage, from the dark web, hacking, spam attacks, phreaking and phishing to information theft, data leaks and cyber-attacks have emerged. And with these latter challenges, a more robust need for effective cybersecurity has gained greater priority and importance than ever before.
The growing threat of the Coronavirus has prompted explorations into the need for heightened cybersecurity as a large number of people across the world have started working remotely from their respective locations via the internet. This threat, unseen at a mass level, was initially ignored. Now it has emerged a threat parallel to Covid-19. The magnitude of this threat is now globally recognized since an exponential growth in hacking attempts has increased dramatically in the last two months.
Hacking attempts are becoming more frequent by the day as more and more people rely on internet connectivity for work and work-related online transactions and communication in an internet-based environment, instead of simply relying on local area networks and intranets installed within the buildings of major offices and away from the internet. At the present and on a global scale, computer or mobile-based applications are being used far more than before to work or study from home via remote connections. This dramatic rise in the use of such software and apps on a global scale has become an ideal situation for cybercriminals to engage in illegal activities. Quite a few of them are exploiting the fears of people, creating uncertainty by bombing virtual apps and social media websites with unsolicited software and malicious links embedded with fake themed Covid-19 alerts or email messages made to look like official communications that can be used to deceive unassuming users in order to gain access and control of their computers or mobile phones.
In these harsher times, you may have witnessed an unprecedented rise in spam emails, messages, voice calls pretending to be from trustworthy organisations like WHO, WEF, NSA or any other organization. Such emails with professionally designed messages may contain links that are actually “phishing” attacks, the largest virtual attacks that most of the cybercriminals use for profiteering or extracting money through cyber-deceit. This technique of deception involves creating clones of web pages and apps popularly used to hack into your social media accounts, internet banking and gain access to other people who are linked with your social accounts to make them easy prey (social engineering). Such attacks may come in different forms such as fake news links, fake calls (phishing attack)—many people often receive fake OTP messages or some come up in apps with capability to launch a malware/Trojan/ransomware in your phone or computer to maliciously steal important data.
As soon as Italy came under the Covid-19 attack, the state announced a complete lockdown enforcing people to take up online services for the smooth functioning of schools, businesses and offices. It was reported that along with the Covid-19 attack, a spike of phishing attacks increased in that month. It makes sense in how cybercriminals tend to exploit everyday people in times of crisis and particularly this one, of a global level. They use such global trends to push users for installation of malware/Trojan by providing obscuring links that are made to appear as if they are from official companies, offices, and software providers with a known brand or recognisable names such as Facebook, Microsoft, the Department of and Motor Vehicles, etc. Recently, a report by law enforcement officials in the US suggested that many websites are selling fake Covid-19 cures, posing as intergovernmental or governmental health organisations in emails with attachments embedded with malware. The malware could control your personal computer and your important documents, with your private pictures landing to the dark side of the internet.
Cybercriminals are not only exploiting human mistakes but also intensifying their efforts to exploit the vulnerabilities that are present in software that we regularly use like WhatsApp, Skype, and Zoom. It is imperative to mention that they are extremely creative in exploiting any vulnerability so that they can have control over a person’s data, network, device or computer or the target may be to take down a targeted organisation. You may have doubts about what these cybercriminals actually achieve. In plain and simple terms, they pursue profiteering or in some cases to take revenge or extort people.

Cybercriminals can have other agendas as well. They may be backed by the government or any organization for sinister objectives. A potential example of such groups would be the hacking group named NSO, a state-sponsored hacking group backed by the Israeli government that developed the spyware called Pegasus. Although, this hacking group poses as an authorised government organization but in past several countries across the world have alleged them for targeted attacks against human rights activists, and journalists. Recently, WhatsApp had a vulnerability which allowed the NSO group to install spyware into a user’s mobile phone just by using the video-calling feature. The vulnerability has been patched but it still exists in older versions of WhatsApp. Many recognized figures like Amazon CEO, Jeff Bezos became easy prey. In India, it was reported that the top politicians, researchers, human rights activists, journalists were targeted using this spyware.
Here you can understand how un-secure one could become when such a group takes control of your mobile phone. Once they get control over your phone, they can turn on your camera; open the mic of your phone, copy data from your file manager or install anything which remains hidden to you or use your phone to target other persons who are linked with your accounts. So if you are still using an older version of WhatsApp, you should immediately update it to the latest version or you can format your mobile phone to prevent further attacks.
More recently, Zoom, a teleconferencing app has sparked a controversy about the app lacking security in ways that could lead to the installation of malicious software. The Zoom vulnerability was exploited by hackers and currently, the Zoom user login database is being sold on the dark web. The app had some vulnerability that allows a malicious attacker to take control of the user’s computer. It is imperative to mention that one should follow the latest guidelines by Zoom to remain secure from attacks like “zoom bombing” etc.
Keep in mind that a cybercriminal can attack any person or an organisation. They can do anything depending on their intentions. They could get your social media account and publicly expose your private pictures or could post anything unwanted or unlawful. They can take your bank details, change the password of your online accounts, and can put malware /Trojan/ransomware running in the background of your system or device.
Whenever you see an unwanted link or any file/software in your email inbox with an attention-grabbing message embedded with it, never click on that link. That link could be a phishing/malware attack for you. If you click on that link, the website seeks some information from you that will help a cybercriminal to guess the important questions that you use to protect your social media accounts. It may trick you to download the software by making you believe you are interacting with the visual interface of a commonly known website, like Facebook, Twitter, Google, Microsoft, Amazon, Flipkart, etc. It is because of these attacks that every user, having an email address, finds a lot of spam emails embedded with attractive messages like “you have won 10,000 USD. Click below on the link and withdraw it into your account.”
With such enticed messages many people become easy targets for hackers. Such emails are simply phishing emails. Currently, the emails that have attractive subject headlines like “Save yourself from Covid-19, click below/download the software.” As such, never click on any link that you are not expecting to receive. Try to practice smart surfing and emailing instead. Moreover, use a firewall, anti-virus software and an anti-spyware programme. Update such software regularly as cybercriminals also exploit the vulnerabilities of older versions in anti-viruses and anti-spyware apps, which is why cybersecurity software developers are constantly patching and updating their apps and sending notifications to their users and subscribers.
At the same time, Covid-19 safety has been used as a means by several governments across the world to establish greater overreach into the privacy of the common people. In some cases, they encourage citizens to install apps that are dumping user data and continue taking the location of a user to keep them under surveillance. In some places, governments may have had already put every citizen under surveillance, but the Covid-19 threat has proven to open legal gates for them to use it as a justification to put citizens under greater surveillance for reasons of “public safety.” Unfortunately, an individual’s privacy has severely tampered within these distressful times.
(The author has co-founded ShafaraCreatives and is a web security analyst. He has contributed to the web security of Google, Yahoo, Facebook, Hackerone and Microsoft. He tweets @islambaduk.)















